Less suspicious with module stomping – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis
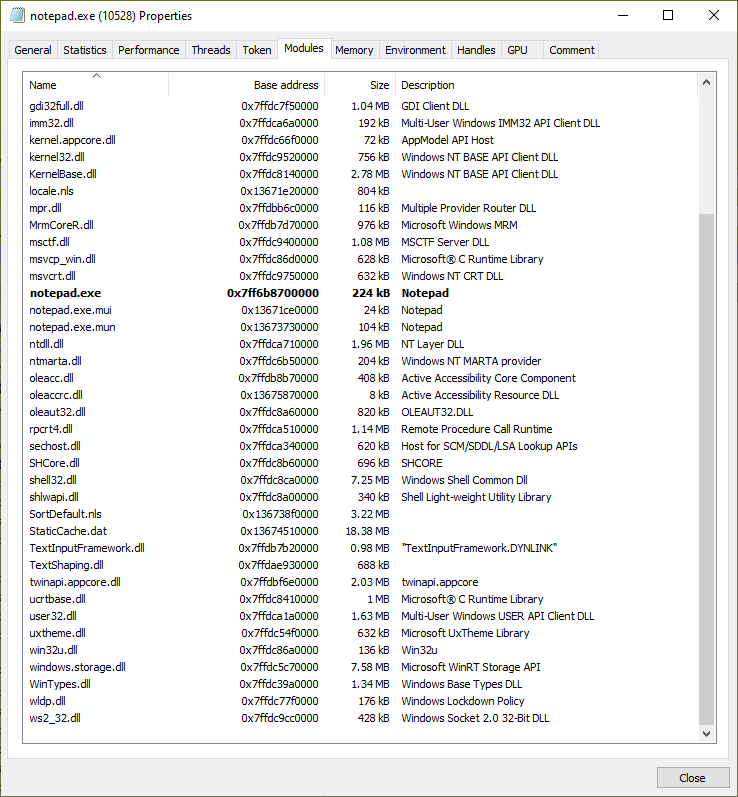
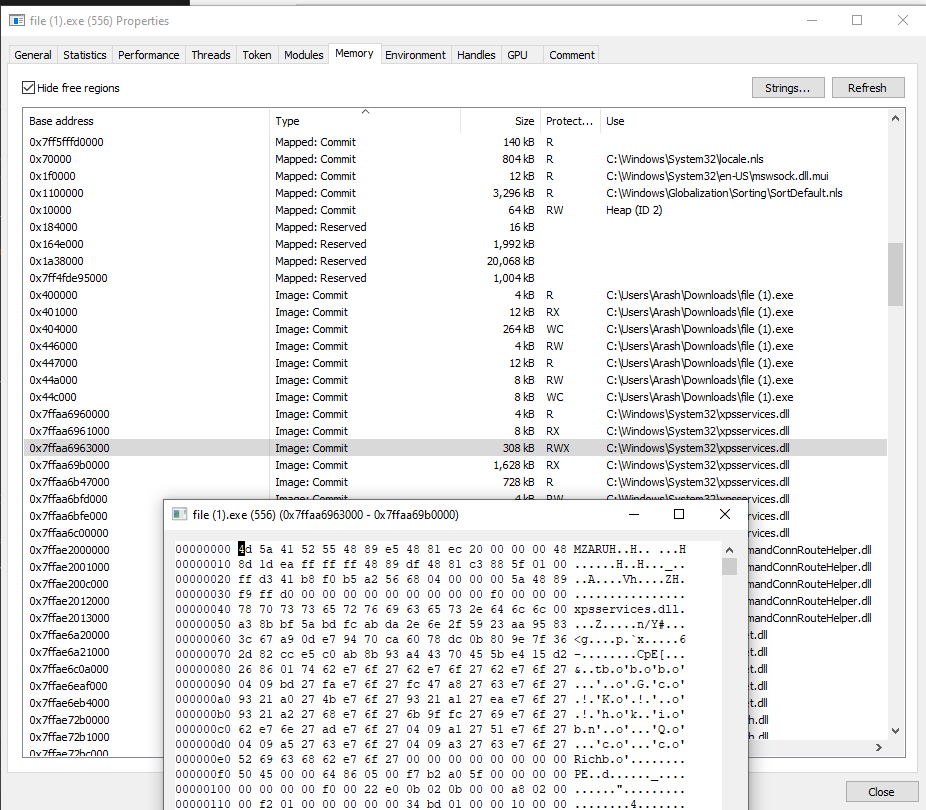
Living Dangerously with Module Stomping: Leveraging Code Coverage Analysis for Injecting into Legitimately Loaded DLLs - ...

Less suspicious with module stomping – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis

OtterHacker on Twitter: "Just adapted @_EthicalChaos_ #ThreadLess injection to work with #Cobalt beacon in pure C. It works really nice ! I mixed it with module stomping to avoid beacon execution from

Less suspicious with module stomping – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis

winterknife 🌻 auf Twitter: „Just released a smol and quick tool to detect module stomping as implemented by Cobalt Strike Might be used to find hollowed dlls in processes using stomp_x64 PoC +
GitHub - WithSecureLabs/ModuleStomping: https://blog.f-secure.com/hiding-malicious-code-with-module-stomping/